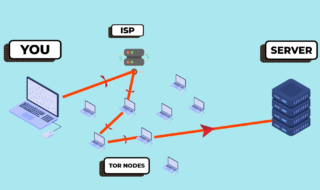
A number of Internet users have switched to a VPN to browse the web securely. A VPN has emerged as a better option when it comes to speed and security. However, a number of people are using TOR too, but VPN is far much better than TOR. It is speedy and allows you to access nearly every restricted website on the web. Still, you need to think whether the VPN you are using is reliable or not? A number of VPN logs the user data.
Moreover, a single VPN server is more vulnerable as compared to two VPN servers connected together. When a VPN server is connected to another VPN that also encrypts the data, it is called a double VPN. Technically, this process if called VPN Cascading. This means that the data transferred by the user using double VPN get encrypted twice before reaching the actual destination. Let us learn more about it.

What is VPN Cascading?
This term may sound a bit complicated to you, but it is easy to get inside your head. VPN Cascading is creating an extra encrypted tunnel to carry the data safely to the end user. In this way, all your web traffic passes through two or more encrypted private tunnels providing an added layer of security. VPN Cascading is really important for the people or organizations looking for top-level security. It can be used by:
- Journalists
- Downloaders
- Financial Institutions
- Governmental Organizations
- E-Commerce Websites
How it works?
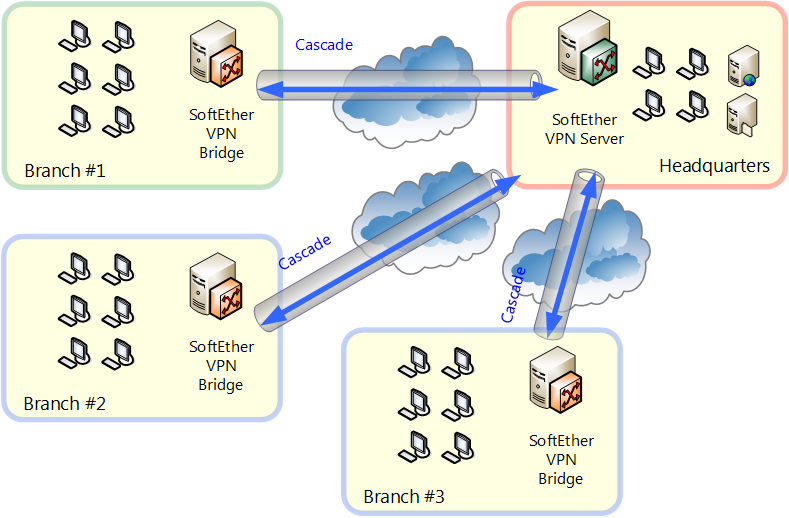
While cascading it, you need to connect two or more encrypted servers at a time. When you connect to a single VPN server, there would be a secure tunnel created between you and the server you keep you away from the prying eyes looking to steal your private data. When you connect to the second encrypted server, you create another encrypted tunnel within the current tunnel of the first server. Though you can connect to as many servers as you want, but practically it is better to go with two tunnels at a time to reduce the latency.
The Virtual Private Network connections might be using different protocols and encryption methods. So, anybody who is trying to intercept the current secure tunnel has to adapt to different encryption methods to find the plain text information. So, if you cascade a Virtual Private Network, it becomes impossible for a hacker or spy to breach the security of both the tunnels.
Is VPN Cascading Good or Bad?
If we talk about in terms of security, Virtual Private Network cascading is good. Even if a spy is able to intercept the security of Virtual Private Network tunnel 1, he/she might not be able to intercept the security of other tunnel(s). Therefore, if you has cascaded the Virtual Private Network, it becomes impossible for any intruder to rob away your personal information.
However, if we have cascaded the servers in a poor way, it can impact the speed significantly. You should always connect the servers that are close to each other by distance to reduce the latency. Moreover, cascading is not made for everyday browsing.
A high level of anonymity is maintained when you have cascaded the Virtual Private Network servers together. Your ISP might see the connection to the first Virtual Private Network server, but will never get to know about the destination IP address as the internet connection is carried through the second Virtual Private Network server.
The second encrypted server will not be able to detect your real IP address as it will be hidden by the first Virtual Private Network server. As your IP addresses changes at every stage of the process, it creates a layering of the anonymity. It is always better to cascade Virtual Private Network if you wish to have more security while browsing the internet. But make sure that you cascade the servers properly.
The End Note
Overall, VPN cascading is one of the safest approaches to browse the Internet. There are not many Virtual Private Network providers who are offering VPN solutions based on this approach. But soon, we will see many companies offering cascaded Virtual Private Network solutions in future. Though it is little slower than normal ones, it is still safer and reliable then most of the available VPNs.