Every time you send files through internet there is a great chance that the files may get intercepted by unethical hackers, which may use these files for their own malicious purposes or even they can use personnel information from the hacked file to perform illegal actions. The information can also be utilized to generate illegal transactions from bank. To avoid this type of information leakage through file, encryption is done, either a secure connection has to be established which may be very costly for a normal person as well as the configuration of the secure connection also becomes a tedious task as well as a very time consuming task.
Amongst the two option suggested above the best method is to use encryption. Encryption may be defined as the method of conversion of normal text which is understandable by any normal being into a complex text which is not understandable by anyone. Without the tools for encryption and decryption the encrypted file is close to being made understandable to a hacker. Each encrypted word has millions of combination that can be made; the encrypted code is known as cipher text. There are multiple types of encryption algorithms available in the IT industry some of which are MD5 and PGP.
PGP
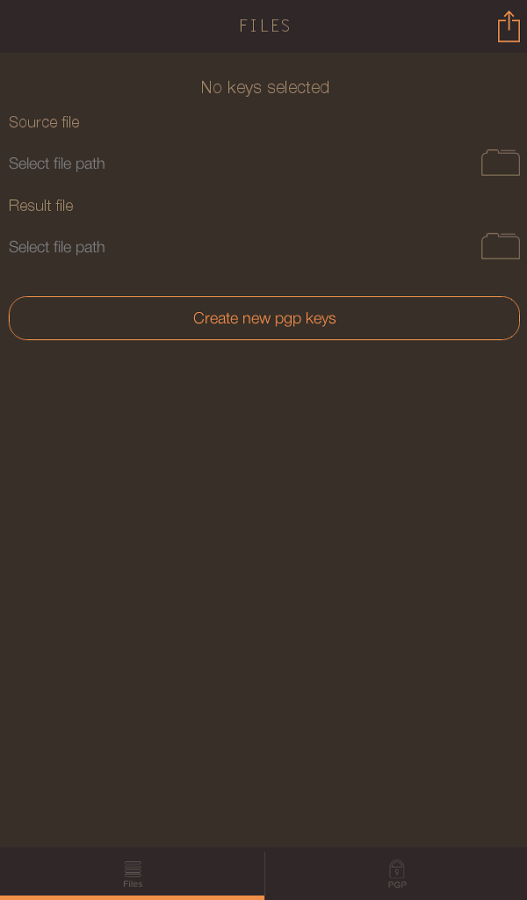
PGP or pretty good privacy which allows you to combine your own personally developed keys to originate a secure file and is amongst the popular encryption methods used by many industries for transaction of data. The developers at SJ Software have developed an application on the android platform to generate encrypted files.
Interested in tweaking you device for better performance then read about it.
STEPS TO GENERATE AN ENCRYPTED FILE
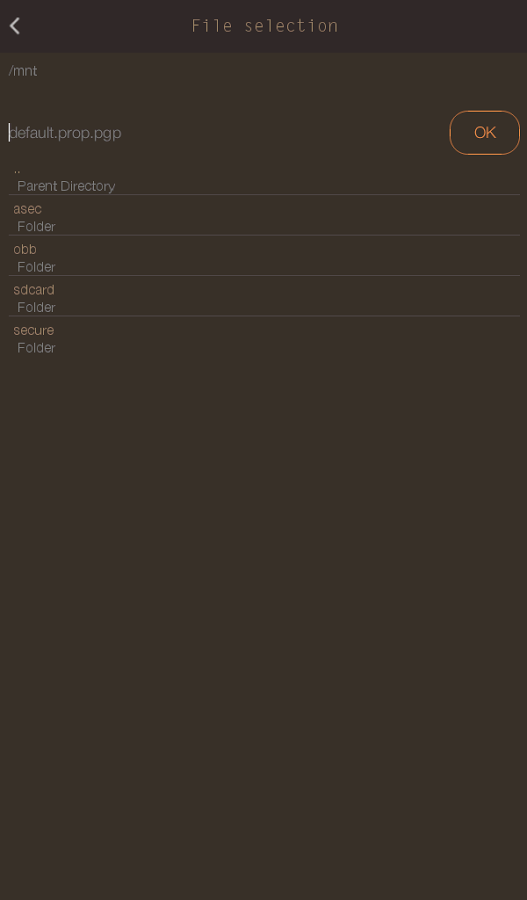
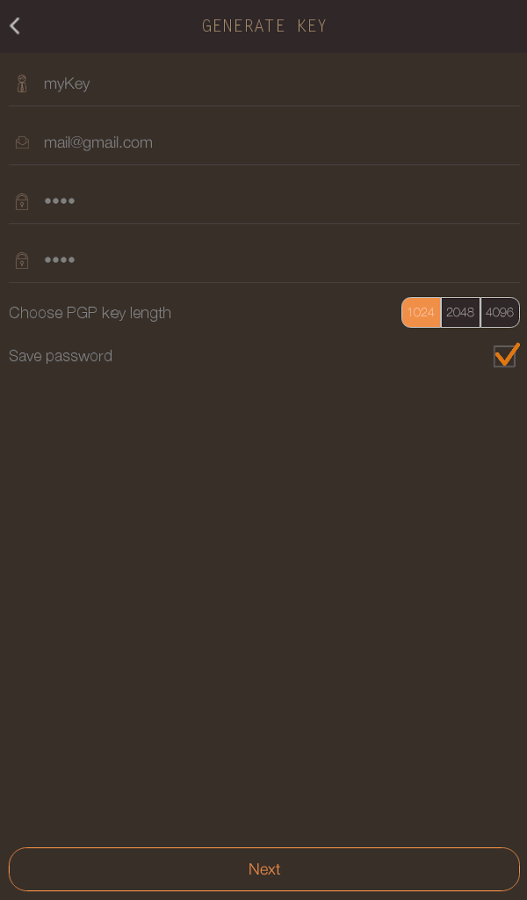
The first step is to generate a private key which is available between the sender and the receiver of the package. The private key plus the public key is utilized to generate the decrypted file which can be easily read. The private key may be generated by the user of the android phone by filling few details required by the software which are easily available. The second step is to generate an encrypted package by selecting a required file to be encrypted, and then to select a private key amongst the generated keys. After these two selections a secure file is generated using a PGP algorithm.
The step for decryption of the encrypted file is also quite similar to that of the generation of an encrypted file. The first step is to import the private key through which the encrypted file is generated. After selecting the imported private key, the file to be decrypted needs to be selected and after the selection of the two steps defined before a decrypted file is generated which may be read by the user. The decryption is also done through the combination of private and public key.
WHY PGP ENCRYPTION
PGP encryption is highly advised to be utilized because the PGP encryption is done in two sub steps, the first step is to utilize the private and public key to generate a combination of words which is not understandable to a normal human the next part of the encryption is to compress the file through which the file being encrypted becomes more complex and is a tedious task for any hacker to hack and interpret what the file actually has the contents as. The compression also allows the reduction of the size of the file which allows the user to send file through the internet in a much lesser time as the all over size becomes less. Other than these two sub steps to generate the encrypted file an arbitrary bit is also added to the file which is generated by the movement of mouse on while the generation of the file, there are also many other methods through which the arbitrary bit can be generated.
To sum all the discussion up I would like to say PGP Files from SJ Softwareis one of the best software for the encryption of files, and is available in the market at a small cost of under 2 $.
Get it from Google PlayStore