Sending and receiving of files have become a regular phase of today’s world. There are many tools available in the market which provides you with fake encryption tools, or tools which are easily hackable by hackers that are online. But, there are some software which genuinely works for the secure transaction between the sender and receiver.
WHAT IS ENCRYPTION ?
Encryption technically may be define as the process of converting normal text written in a file in a complex text which is not understandable by the common people if they receive the file by mistake or are able to hack the transaction of the file. The file which has been converted into a special text can only be converted by a special key which is a mixture of a private and a public key. The public key is available openly to everyone on the internet which contains basic protocols or rules that are required to de complex the information in the file. The private key contains specific rules which are developed due to different actions done by the maker of the private key that is the author of the key mostly that is the user of the software. The private key is shared with the receiver of the encrypted file. As told before the combination of the private and the public can decrypt the text file which was previously encrypted the sender and the receiver should also have the same software for doing this tedious task which in the eye of the user is a matter of some clicks.
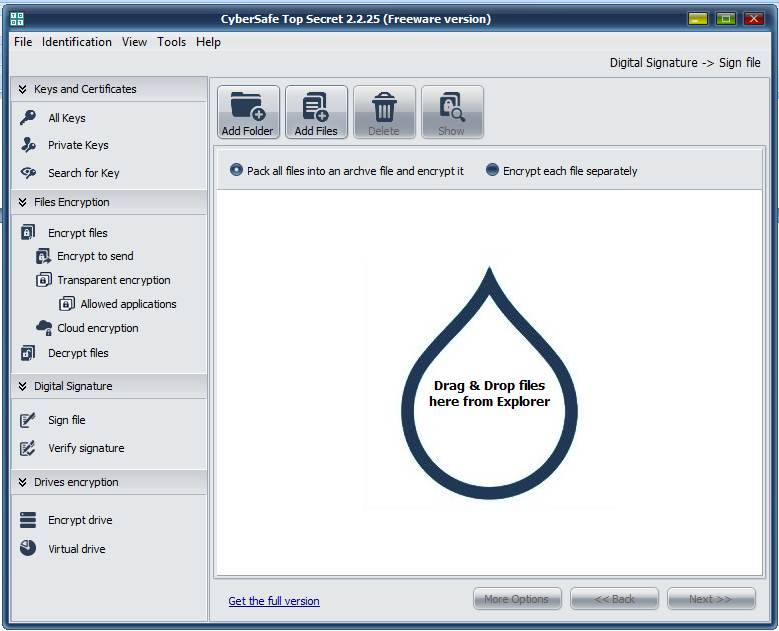
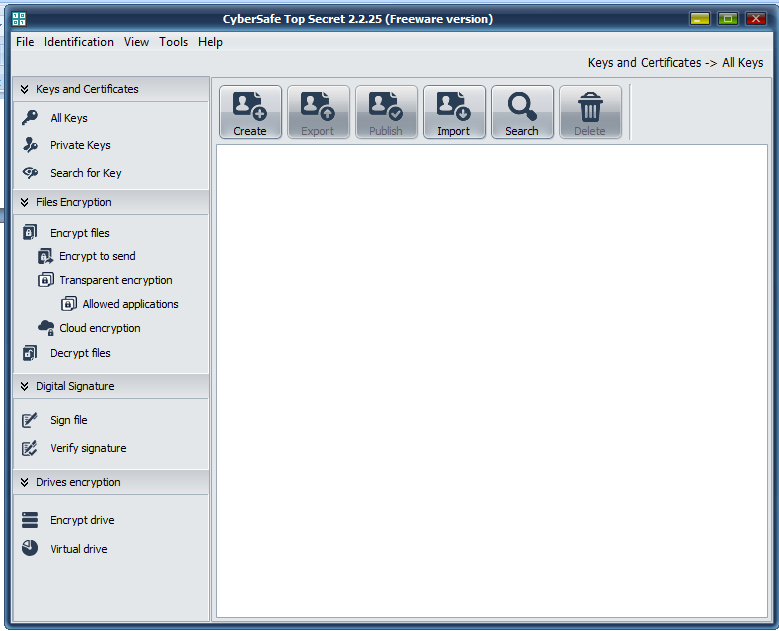
CYBERSAFE TOP SECRET: ENCRYPTION SOFTWARE
 The package is a very small downloadable file which provides you with a graphical user interface or GUI which can be utilized by the user to create encrypted files in a matter of minutes. It also contains the ability of creating keys that are being authorized and certified by the user of the program through the email address provided by the user of the software who is creating the key, there are multiple type of encryption that is allowed by the package as well as by varying number of password keys which allows the user to have a flexibility of words to authorize as the password of the encrypted file being sent over the internet. It should be noted that the more number of password character the more time it takes to get it decrypted by any malicious software. Each set of characters that can be used as the password has its own identity in the computer world, and to find that specific identity a variety of 1 million of combination has to be checked with the file.
The package is a very small downloadable file which provides you with a graphical user interface or GUI which can be utilized by the user to create encrypted files in a matter of minutes. It also contains the ability of creating keys that are being authorized and certified by the user of the program through the email address provided by the user of the software who is creating the key, there are multiple type of encryption that is allowed by the package as well as by varying number of password keys which allows the user to have a flexibility of words to authorize as the password of the encrypted file being sent over the internet. It should be noted that the more number of password character the more time it takes to get it decrypted by any malicious software. Each set of characters that can be used as the password has its own identity in the computer world, and to find that specific identity a variety of 1 million of combination has to be checked with the file.
VARIETY OF PACKAGES
There is a wide variety of exe packages that you may download from the website. The URL of the website is http://cybersafesoft.com/products/topsecret/it should be noted that each of the downloaded from the above mentioned URL has its own unique features, please consider the contents of each package before buying and downloading the package. There is an availability of a free version which has many limitations to it but still allows you to test in order to understand the proper working of the software and to also test if it fulfill your needs or not. Though there are still some part of the software that you will not be able to test on the free version of the software, like the encryption of the network folders is not available in the free package but still you are able to get a fare idea of how the software works. It should be noted that for new users in the field off encrypting and security video tutorials have been made available to understand the working of the software.
FEATURES OF SOFTWARE
As mentioned before each package comes with a different feature enabled in it but there are some basic features that are available on each of the packages.
- Private keys: the user of the software is allowed to develop his/her own private key which can be used to encrypt the file.
- Drive Encryption: there is also a feature of encrypting of a whole drive which may be only opened by the use of the password associated with it while the encryption of the drive with the key developed by the user
- Virtual Drive Encryption: following the same steps above even a virtual drive can be encrypted and can be later opened with the password associated with the drive during encryption.
Available OS
- Windows XP| Vista| 7|8|8.1|10
Money back guarantee
If you are unsatisfied within first 30 days of premium version, just submit a support ticket to get your full refund.
Final thought
Cybersafe top secret seems to be the best ever solution to keep all the sensitive files in our system.