The issue of confidentiality is one of the most important for business, especially if we are talking about big companies. Data leakage is fraught with many consequences, including loss of competitiveness. If your project falls into the wrong hands, then another company will release a unique product and gain an advantage in the market. As a result, it threatens financial disaster for you and your employees, and in some cases even bankruptcy. In our opinion, using dataroom software is the best solution for keeping data safe. Let’s talk about the importance of data privacy for business success.
Contents
The First Steps in a Nutshell
It would seem that everything is simple – important documents must be stored in an inaccessible place and protected from encroachment by competitors. However, as a rule, the greatest threat to the business is not the intrigues of competitors, but the employees of your enterprise. Their negligence and indiscretion often cause data leakage or the loss of important documents. At the same time, the main mistake that many managers make is the lack of a systematic approach to protecting information. To prevent this from happening in your company, it is important to follow a few simple rules.
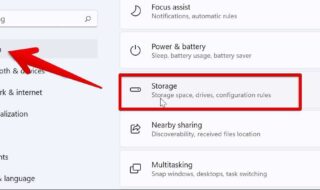
- Analyze the best virtual data rooms. This will help you choose the best digital storage tool for your data. At the same time, you, as the owner of the company, can set up access and edit the list of people who can access the information.
- Determine the list of confidential information. To reduce the risks of disclosure of confidential information, the company should assess the scale of threats and losses from data loss.
- Differentiate access rights. All employees of the company can be conditionally divided into four groups: senior managers, middle managers, line managers, as well as service and technical personnel. All categories of workers should have different amounts of information.
- Perform data room comparison. Do not rush to use the first service you see on the Internet. Read customer reviews, compare prices and packages before making a decision.
- Develop an information security policy. The security policy should be the result of a collaborative effort between the finance professional, the commercial director, the head of the IT service, and the heads of subsidiaries (if any).
- Set fines for disclosure of classified data. Responsibility for non-compliance with established regulations should be spelled out in the job descriptions of employees and the employment contract. In addition, at many enterprises, an extra agreement on non-disclosure of confidential information is mandatory signed with employees.
Today, security issues are solved in the digital space — that’s why data room services are so popular. You can set the number of people who have access to information and be sure of the confidentiality of this data. It is convenient and corresponds to modern trends in the world of technology. You end up with a competitive edge and powerful tool for database storage and modification.
Types of Risks and Threats to Information Security

Security threats identified by you or your employees need to be systematized. Business confidentiality is a delicate issue requiring an integrated approach. It is especially important to perform VDR due diligence when choosing a data storage service. Information security directly affects the company’s reputation, so you also need to divide the likely reputational threats into several categories.
| Technical risks | Incidents occur during software failures or device failures. This also includes information security, including the safety of personal data and the privacy of correspondence. |
| Human factor | Employee negligence, poor management decisions, and negative customer reviews about the product or service received. |
| Economic risks | Tax penalties or cooperation with partners with an unreliable reputation. |
Some of the listed reasons depend on the actions of the head or employees of the company, but some relate to external factors. For example, you cannot influence the actions of your competitors, but you can use tools to prevent the leakage of important information. In any case, the data room tool can become a “safety raft” and help maintain a positive reputation.
Confidentiality is the Key to a Trusting Relationship with the Client
The main principle of confidentiality is that no one should know more than they are supposed to. Clients and employees who are not directly involved in the processing of information receive only the data that they need to complete the task. The decision on what to classify as a trade secret is made by the entrepreneur independently. To ensure the protection of confidential information that is classified as a trade secret, the following measures can be taken:
- A list of information that is related to a trade secret is compiled. This information is transferred to a digital data room with access for a limited number of users. For example, you can store data of the following nature: a list of customers, contacts of suppliers, the markup on goods, etc.
- Access restriction is introduced. The procedure for obtaining access and monitoring compliance with this order is established. For example, if an employee works with suppliers, they do not need to know about all the company’s data. Accordingly, for such an employee, access to information that does not contain information about suppliers should be restricted.
- A record of persons having access to information constituting a trade secret is maintained. It is necessary to separately keep records of persons who work in the company, and persons who have received access to data on other grounds. You can use VDR software to set up access for your company’s employees.
- Drafting a legal contract. The use of information constituting a commercial secret is regulated by employment contracts, which stipulate the responsibility of persons for the disclosure of data.
In some cases, a separate confidentiality agreement should be created. The document includes the basic principles of the company’s confidentiality, features, and rules for the collection, storage, and subsequent use of personal data. The document should be publicly available so that potential clients or colleagues are aware of these principles. However, data that is not intended for everyone should be stored in a secure place, such as an electronic data room.